Kong Event Gateway
Introducing Kong Event Gateway
Kong Event Gateway is a lightweight, fast, and flexible cloud-native event streaming proxy. It sits between Kafka clients and backend Kafka clusters.
With its extensible policy engine, you can adapt Kafka to your requirements-transforming, encrypting, and monitoring messages through a central proxy to add governance, enable multi-tenancy, and strengthen security.
Kong Event Gateway runs in front of any Kafka cluster and can be extended through policies.


Install Event Gateway
You can configure Event Gateway using Konnect.
Before deploying Event Gateway, ensure that you have a Kafka cluster.
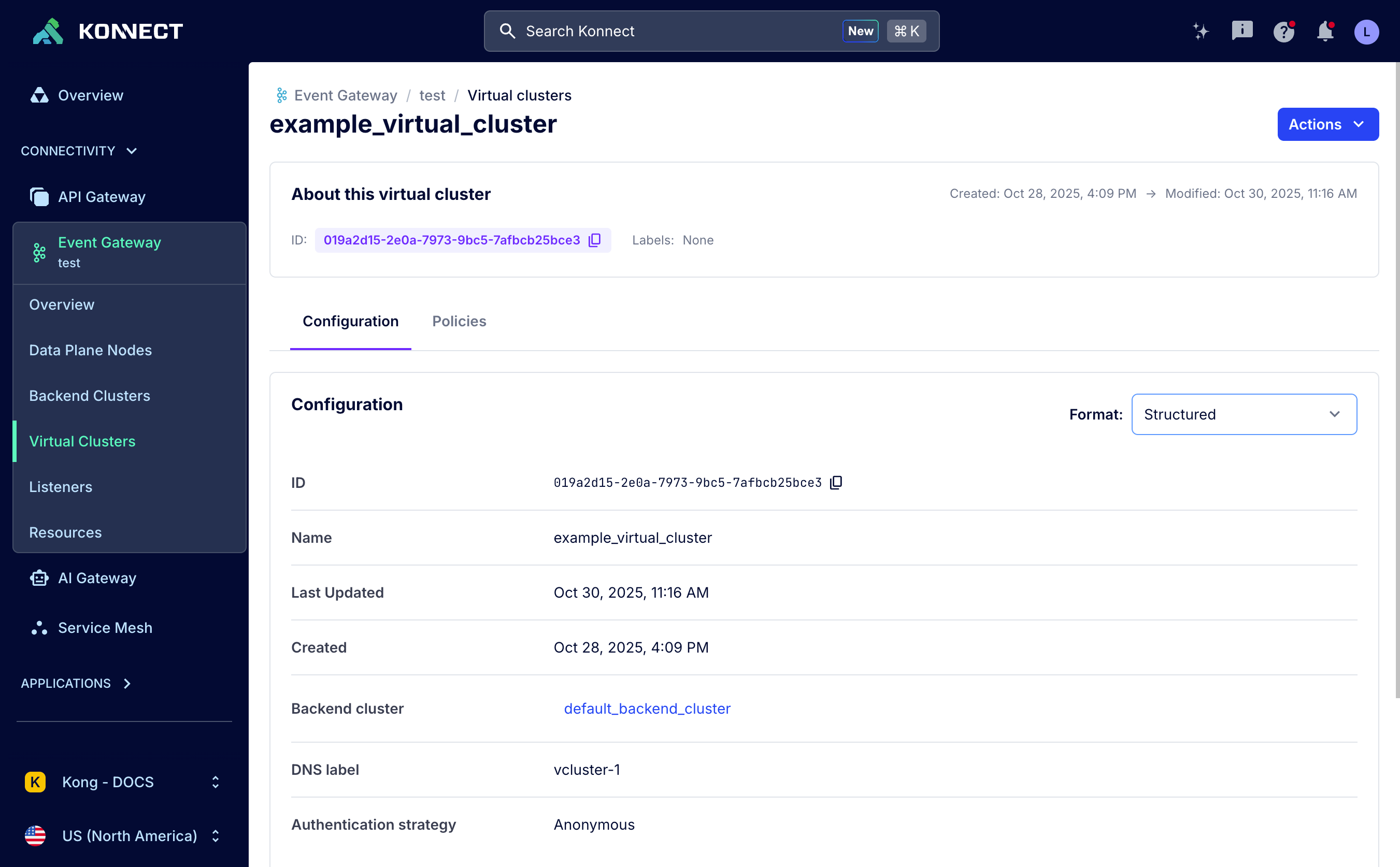
Kong Event Gateway in the Konnect UI
Konnect lets you manage, connect to, and monitor the status of all Kong Event Gateway control planes (CPs) and data plane nodes (DPs) in one place.
Key features include:
- Manage control planes and their configurations
- Deploy and monitor data plane nodes
- Find backend clusters, virtual clusters, listeners, and resources directly in a control plane’s sidebar
- Create and manage policies through the Virtual Clusters and Listeners sections
Use cases for Kong Event Gateway
|
Use case
|
Outcomes
|
Features
|
How-to guide or example
|
|---|---|---|---|
| Govern Kafka to enforce security and guidelines in an automated fashion | Centrally manage and instantly update access control policies without touching individual brokers | ACL policy | Get started with Event Gateway and ACLs |
| Replace legacy auth methods with modern enterprise identity standards your team already uses | OAuth | Set up Event Gateway with Kong Identity OAuth | |
| Know exactly which teams and topics are driving cluster load, in real time, via in-platform dashboards or exported to your preferred tooling | Observability | Configure observability with OpenTelemetry | |
| Demonstrate compliance with data privacy regulations through auditable, enforceable controls | Encryption policy and Decryption policy | Encrypt and decrypt Kafka messages | |
| Simplify your Kafka deployment because it’s too complicated and expensive | Isolate teams or environments on a shared cluster without complex infrastructure duplication | Virtual clusters | Set up virtual clusters |
| Automatically enforce access rules based on identity metadata with no manual ACL management | OAuth | Set up Event Gateway with Kong Identity OAuth | |
| Improve the developer experience to increase adoption and achieve faster time-to-value | Prevent malformed messages from ever reaching consumers |
Schema validation - produce phase
Schema validation - consume phase |
Ensure data quality with schema validation |
| Onboard apps using OAuth flows developers already know, with no Kafka expertise required | OAuth | Set up Event Gateway with Kong Identity OAuth | |
| Let any developer produce and consume Kafka events using standard REST - no Kafka client needed | Protocol mediation | – | |
| Productize Kafka data into “data products” with self-service access that you can monetize | Package raw topic data into clean, audience-specific products without duplicating data | Namespaces | Set up namespaces and enforce access control with ACLs |
| Ensure each consumer only sees the records they’re entitled to, enforced automatically | Modify Headers policy and Skip Records policy | Filter Kafka records by classification headers |
Tools to manage Kong Event Gateway
- Konnect UI: Manage Event Gateway entities within Konnect control planes using a UI.
- Control Plane API: Manage Event Gateway entities within Konnect control planes via an API.
- Terraform: Manage infrastructure as code and automated deployments to streamline setup and configuration of Konnect and Kong Event Gateway.
Authentication
Flexible authentication for both virtual cluster client connections and backend cluster access
Hostname mapping
Map gateway servers to upstream Kafka brokers using port mapping or SNI routing
Expressions language reference
Learn about the expressions language used in Kong Event Gateway for conditional fields
API reference
Explore the reference documentation for all Kong Event Gateway APIs
Data plane configuration reference
Explore the reference documentation for all Kong Event Gateway data plane configuration parameters
Entities and resources
See all the entities that make up Kong Event Gateway and its ecosystem
Frequently asked questions about Kong Event Gateway
How is Kong Event Gateway deployed?
The Kong Event Gateway data planes are self-managed and deployed by you, the user. The Kong Event Gateway control plane is part of the Kong Konnect platform.
Does Kong Event Gateway run on-prem?
No, Kong Event Gateway is only available through the Kong Konnect platform.
Can I proxy multiple Kafka clusters?
Yes, the gateway can proxy multiple backend clusters, though only one can currently be proxied in a single client connection.
How-to Guides
- Set up observability for Kong Event Gateway View →
- Configure SNI routing with Kong Event Gateway View →
- Encrypt and decrypt Kafka messages with Kong Event Gateway View →
- Filter Kafka records by classification headers View →
- Get started with Kong Event Gateway View →
- Set up Kong Event Gateway with Kong Identity OAuth View →
- Productize Kafka topics with Kong Event Gateway View →
- View More →
Looking for HTTP over Kafka? Check out the Kong Gateway protocol mediation plugins.